“Cyber-attacks” across all industries, social media, and even the government are now an everyday occurrence. Oftentimes, these attacks are classified under the umbrella of “hacking”, but there are key aspects to consider when classifying a “hack”. Did the attack come from the inside or the outside? What method did they use to hack into the computer system? How can this be prevented? This blog explores three examples of how quickly a “hack” can be performed and how damaging it can be to you, your business, and your customers. Hackers target both computers and the data they contain. First, we’ll review an attack performed by someone who has access to the computer, the classic Buffer Overflow. Then, an attack on a computer’s data from the outside, a SQL injection. And finally, XREF and XSS attack websites that computers may access. Each of these hacks is fairly straightforward to implement, sometimes taking only a few minutes to perform.
Buffer Overflow – Attacking a Computer’s Memory
The Buffer Overflow attack is one of the oldest types of attacks. It is aptly named for when a hacker “overflows” beyond a “buffer” of memory that they have been provided. When you start a computer program, information is loaded into short-term memory. On top of this memory is the “stack” which is used by the computer to control the flow of what happens next. This stack can be overwritten by intentionally grabbing more memory “buffer” than requested; in effect “overflowing” to where it shouldn’t.
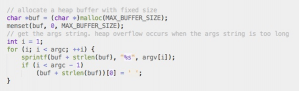
A hacker accomplishes this by running a few short lines of commands referred to as “code” to misleadingly tell the computer it wants space allocated in memory a certain size; a buffer. to the program then intentionally goes above and beyond that amount and “overflows” into the computer’s stack where it can get full access to the system! This attack can come from many directions: an employee in a company, browsing the internet, or even purchasing an item online. On the internet, this attack can occur by simply looking at images on a website. When the computer reads and displays the miss-sized image, it overloads the allocated memory and runs the malicious code. The Buffer Overflow attack can even be performed on an everyday consumer product device: such as the attack found this year on the highest selling gaming console. In this case, the hacker only needed physical access to the device, in the form of a portable gaming machine containing user account and payment information. Below is a piece of an outdated Buffer Overflow test attack that is easily protected against by upgrading a computers software library.There are well-known defenses to this attack including allowing only certain programs access to key areas of memory and randomizing where in memory the stack resides. The best defense for this attack to keep your software updated and developer tools updated with the latest libraries that should be able to prevent these types of hacks.
SQL Injection – Attacking a Computer’s Database
Typically, information is temporarily stored in a computer’s memory while it’s being used. However, information that has to be saved for future use usually resides in some type of database. So, it’s no surprise that a database containing information like customer names, addresses, SSN’s, and bank accounts are often high priority targets for a hacker. SQL Injection slips in additional commands when reading information from a database. This can occur on any website requiring user input. For example, your username and password. Instead of typing a valid password, the hacker instead enters a special escape command such as “/*”, “//”, or “–“ followed by a second command such as the one below that deletes all existing password information and allows full system access.
“; * drop password_table, select * from password”
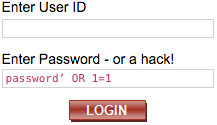
Just as with the Buffer Overflow attack, there exist basic defenses; checking the input for inserted commands, or only allowing certain activities, like read-only access.
Web Scripting – Attacking a Website
While Buffer Overflow and SQL Injection are easy to implement, the next set of attacks require a bit of finesse. They involve hijacking a user while they surf the web. The two most popular such attacks are Cross-Site Request Forgery (XSRF or CSRF) and Cross-Site Scripting (XSS). Cross-Site Request Forgery is hijacking a user’s web browsing. This can occur when you log into a vulnerable website and don’t log out or close your browser. Subsequently, when you visit a site which contains the attack, the attacking site can then secretly read information from the first website and perform activities using as if it were you (like making an expensive purchase).
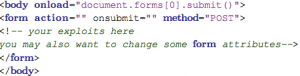
Cross-Site Scripting is a bit simpler and occurs when an attacker puts the code into a vulnerable website that is then activated by simply visiting the website. This hack could lurk in the comments section of a news or social website where the hacker enters a comment with the hidden hack. Just by viewing the page, the user may unknowingly run the hack. The hack could capture information about the user which is then passed along to the hacker. Again, defenses exist such as special coded tokens to identify a user and stop XSRF attacks, or by blocking a hacker from entering XSS attack code in the comments. Here is an example below:The defense for this type of hack is largely dependent on the website taking proactive action on behalf of their users. If your site is open to consumers, it’s your responsibility to take the necessary steps to limit user exposure to scripting attacks, implementing regular audits, or limiting the amount of scripting done on the user’s behalf.
All of these attacks are easy to implement and are devastatingly effective, but they are also very straightforward to defend against. In the age of persistent cyber-attacks, companies must remain vigilant in protecting their computing resources to prevent significant financial and reputational degradation. While this blog focused on hacks implemented by writing software code, these types of hacks are just one of many Information Security threats an organization faces, along with email phishing, viruses, network denial of service, etc. The most effective form of protection for a company is the rapid implementation of basic defenses combined with education of both internal employees and external users on the importance of safe information practices. After an initial assessment of the risks, a company can mature from the basic hardening of their security defenses to fend off casual attacks to more thorough protections in an effort to thwart the most sophisticated hackers.



